▍ FreeIPA¶
Настройка централизованного управления учетными записями пользователей¶
С увеличением количества всяких железок и виртуальных серверов в домашней лаборатории встала задача централизованного управления пользователями, чтобы каждый раз их не создавать на всех новых местах будем настраивать FreeIPA на Альт Сервер 10. У него в отличии от OpenLDAP есть удобная веб морда для создания пользователей и групп.
Сервер FreeIPA – это система. Аналог Active Directory для Linux. Однако, помимо сервера LDAP (на базе 389 Directory Server) сервер FreeIPA включает в себя еще следующий набор возможностей:
Аутентификация Kerberos (MIT’s Kerberos 5). Встроенный сервер DNS (BIND). Встроенный центр сертификации (DogTag).
Вводная часть¶
В качестве домена будем использовать HOME.LAB
| ip | hostname | role | OS |
|---|---|---|---|
| 192.168.0.2 | ipa.home.lab | FreeIPA сервер | ALT Virtualization Server 10.1 (Actinoform) |
| 192.168.0.4 | client1.home.lab | client1 + XRDP | ALT Workstation K 10.2 (Sorbaronia Mitschurinii) |
| 192.168.0.44 | synology.home.lab | Synology | DSM 7.2.1-69057 Update 1 |
Настройка FreeIPA сервера¶
За основу было взято официальное руководство
Для корректной работы сервера необходимо, задать ему полное доменное имя (FQDN). Имя серверу можно назначить командой:
[!IMPORTANT] IP-адрес сервера не должен изменяться..
Так как я использовал чистую установку Альт сервера то шаги с удалением ahttpd я пропустил, иначе потребуется выполнить:
Для ускорения установки можно установить демон энтропии haveged:
Ставим сам FreeIPA сервер и DNS:
Теперь запускаем интерактивную настройку FreeIPA
# ipa-server-install
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
Version 4.9.11
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (CHRONY)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure SID generation
* Configure the KDC to enable PKINIT
To accept the default shown in brackets, press the Enter key.
Do you want to configure integrated DNS (BIND)? [no]: yes
Enter the fully qualified domain name of the computer
on which you're setting up server software. Using the form
<hostname>.<domainname>
Example: master.example.com
Server host name [ipa.home.lab]:
Warning: skipping DNS resolution of host ipa.home.lab
The domain name has been determined based on the host name.
Please confirm the domain name [home.lab]:
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [HOME.LAB]:
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password:
Password (confirm):
The IPA server requires an administrative user, named 'admin'.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
Checking DNS domain home.lab., please wait ...
Invalid IP address fe80::1111:ff:111:a4fb for ipa.home.lab: cannot use link-local IP address fe80::1111:ff:111:a4fb
Do you want to configure DNS forwarders? [yes]: yes
Following DNS servers are configured in /etc/resolv.conf: 192.168.0.200
Do you want to configure these servers as DNS forwarders? [yes]: yes
All detected DNS servers were added. You can enter additional addresses now:
Enter an IP address for a DNS forwarder, or press Enter to skip:
DNS forwarders: 192.168.0.200
Checking DNS forwarders, please wait ...
Do you want to search for missing reverse zones? [yes]: yes
Reverse record for IP address 192.168.0.2 already exists
Trust is configured but no NetBIOS domain name found, setting it now.
Enter the NetBIOS name for the IPA domain.
Only up to 15 uppercase ASCII letters, digits and dashes are allowed.
Example: EXAMPLE.
NetBIOS domain name [HOME]:
Do you want to configure CHRONY with NTP server or pool address? [no]:
The IPA Master Server will be configured with:
Hostname: ipa.home.lab
IP address(es): 192.168.0.2
Domain name: home.lab
Realm name: HOME.LAB
The CA will be configured with:
Subject DN: CN=Certificate Authority,O=HOME.LAB
Subject base: O=HOME.LAB
Chaining: self-signed
BIND DNS server will be configured to serve IPA domain with:
Forwarders: 192.168.0.200
Forward policy: only
Reverse zone(s): No reverse zone
Continue to configure the system with these values? [no]: yes
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Развернуть
Adding [192.168.0.2 ipa.home.lab] to your /etc/hosts file
Disabled p11-kit-proxy
Configuring NTP daemon (chronyd)
[1/4]: stopping chronyd
[2/4]: writing configuration
[3/4]: configuring chronyd to start on boot
[4/4]: starting chronyd
Done configuring NTP daemon (chronyd).
Successfully synchronized time with CHRONY
Configuring directory server (dirsrv). Estimated time: 30 seconds
[1/42]: creating directory server instance
Validate installation settings ...
Create file system structures ...
Perform SELinux labeling ...
selinux is disabled, will not relabel ports or files.
Create database backend: dc=home,dc=lab ...
Perform post-installation tasks ...
[2/42]: tune ldbm plugin
[3/42]: adding default schema
[4/42]: enabling memberof plugin
[5/42]: enabling winsync plugin
[6/42]: configure password logging
[7/42]: configuring replication version plugin
[8/42]: enabling IPA enrollment plugin
[9/42]: configuring uniqueness plugin
[10/42]: configuring uuid plugin
[11/42]: configuring modrdn plugin
[12/42]: configuring DNS plugin
[13/42]: enabling entryUSN plugin
[14/42]: configuring lockout plugin
[15/42]: configuring graceperiod plugin
[16/42]: configuring topology plugin
[17/42]: creating indices
[18/42]: enabling referential integrity plugin
[19/42]: configuring certmap.conf
[20/42]: configure new location for managed entries
[21/42]: configure dirsrv ccache and keytab
[22/42]: enabling SASL mapping fallback
[23/42]: restarting directory server
[24/42]: adding sasl mappings to the directory
[25/42]: adding default layout
[26/42]: adding delegation layout
[27/42]: creating container for managed entries
[28/42]: configuring user private groups
[29/42]: configuring netgroups from hostgroups
[30/42]: creating default Sudo bind user
[31/42]: creating default Auto Member layout
[32/42]: adding range check plugin
[33/42]: creating default HBAC rule allow_all
[34/42]: adding entries for topology management
[35/42]: initializing group membership
[36/42]: adding master entry
[37/42]: initializing domain level
[38/42]: configuring Posix uid/gid generation
[39/42]: adding replication acis
[40/42]: activating sidgen plugin
[41/42]: activating extdom plugin
[42/42]: configuring directory to start on boot
Done configuring directory server (dirsrv).
Configuring Kerberos KDC (krb5kdc)
[1/10]: adding kerberos container to the directory
[2/10]: configuring KDC
[3/10]: initialize kerberos container
[4/10]: adding default ACIs
[5/10]: creating a keytab for the directory
[6/10]: creating a keytab for the machine
[7/10]: adding the password extension to the directory
[8/10]: creating anonymous principal
[9/10]: starting the KDC
[10/10]: configuring KDC to start on boot
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring ipa-custodia
[1/5]: Making sure custodia container exists
[2/5]: Generating ipa-custodia config file
[3/5]: Generating ipa-custodia keys
[4/5]: starting ipa-custodia
[5/5]: configuring ipa-custodia to start on boot
Done configuring ipa-custodia.
Configuring certificate server (pki-tomcatd). Estimated time: 3 minutes
[1/29]: configuring certificate server instance
[2/29]: stopping certificate server instance to update CS.cfg
[3/29]: backing up CS.cfg
[4/29]: Add ipa-pki-wait-running
[5/29]: secure AJP connector
[6/29]: reindex attributes
[7/29]: exporting Dogtag certificate store pin
[8/29]: disabling nonces
[9/29]: set up CRL publishing
[10/29]: enable PKIX certificate path discovery and validation
[11/29]: authorizing RA to modify profiles
[12/29]: authorizing RA to manage lightweight CAs
[13/29]: Ensure lightweight CAs container exists
[14/29]: Ensuring backward compatibility
[15/29]: starting certificate server instance
[16/29]: configure certmonger for renewals
[17/29]: requesting RA certificate from CA
[18/29]: publishing the CA certificate
[19/29]: adding RA agent as a trusted user
[20/29]: configure certificate renewals
[21/29]: Configure HTTP to proxy connections
[22/29]: updating IPA configuration
[23/29]: enabling CA instance
[24/29]: importing IPA certificate profiles
[25/29]: migrating certificate profiles to LDAP
[26/29]: adding default CA ACL
[27/29]: adding 'ipa' CA entry
[28/29]: configuring certmonger renewal for lightweight CAs
[29/29]: deploying ACME service
Done configuring certificate server (pki-tomcatd).
Configuring directory server (dirsrv)
[1/3]: configuring TLS for DS instance
[2/3]: adding CA certificate entry
[3/3]: restarting directory server
Done configuring directory server (dirsrv).
Configuring ipa-otpd
[1/2]: starting ipa-otpd
[2/2]: configuring ipa-otpd to start on boot
Done configuring ipa-otpd.
Configuring the web interface (httpd)
[1/24]: stopping httpd
[2/24]: backing up ssl.conf
[3/24]: disabling nss.conf
[4/24]: configuring mod_ssl certificate paths
[5/24]: setting mod_ssl protocol list
[6/24]: configuring mod_ssl log directory
[7/24]: disabling alt mod_ssl defaults
[8/24]: disabling mod_ssl OCSP
[9/24]: adding URL rewriting rules
[10/24]: configuring httpd
Nothing to do for configure_httpd_wsgi_conf
[11/24]: configuring httpd modules
[12/24]: setting up httpd keytab
[13/24]: configuring Gssproxy
[14/24]: setting up ssl
[15/24]: configure certmonger for renewals
[16/24]: publish CA cert
[17/24]: clean up any existing httpd ccaches
[18/24]: enable ccache sweep
[19/24]: configuring SELinux for httpd
[20/24]: create KDC proxy config
[21/24]: enable KDC proxy
[22/24]: starting httpd
[23/24]: configuring httpd to start on boot
[24/24]: enabling oddjobd
Done configuring the web interface (httpd).
Configuring Kerberos KDC (krb5kdc)
[1/1]: installing X509 Certificate for PKINIT
Done configuring Kerberos KDC (krb5kdc).
Applying LDAP updates
Upgrading IPA:. Estimated time: 1 minute 30 seconds
[1/10]: stopping directory server
[2/10]: saving configuration
[3/10]: disabling listeners
[4/10]: enabling DS global lock
[5/10]: disabling Schema Compat
[6/10]: starting directory server
[7/10]: upgrading server
Could not get dnaHostname entries in 60 seconds
Could not get dnaHostname entries in 60 seconds
[8/10]: stopping directory server
[9/10]: restoring configuration
[10/10]: starting directory server
Done.
Restarting the KDC
dnssec-validation yes
Configuring DNS (named)
[1/13]: generating rndc key file
[2/13]: adding DNS container
[3/13]: setting up our zone
[4/13]: setting up our own record
[5/13]: setting up records for other masters
[6/13]: adding NS record to the zones
[7/13]: adding dns ntp record
[8/13]: setting up kerberos principal
[9/13]: setting up named.conf
created new /etc/bind/named.conf
created named user config '/etc/bind/ipa-ext.conf'
created named user config '/etc/bind/ipa-options-ext.conf'
created named user config '/etc/bind/ipa-logging-ext.conf'
[10/13]: setting up server configuration
[11/13]: configuring named to start on boot
[12/13]: changing resolv.conf to point to ourselves
[13/13]: disable chroot for bind
Done configuring DNS (named).
Restarting the web server to pick up resolv.conf changes
Configuring DNS key synchronization service (ipa-dnskeysyncd)
[1/7]: checking status
[2/7]: setting up bind-dyndb-ldap working directory
[3/7]: setting up kerberos principal
[4/7]: setting up SoftHSM
[5/7]: adding DNSSEC containers
[6/7]: creating replica keys
[7/7]: configuring ipa-dnskeysyncd to start on boot
Done configuring DNS key synchronization service (ipa-dnskeysyncd).
Restarting ipa-dnskeysyncd
Restarting named
Updating DNS system records
Configuring SID generation
[1/8]: creating samba domain object
[2/8]: adding admin(group) SIDs
[3/8]: adding RID bases
[4/8]: updating Kerberos config
'dns_lookup_kdc' already set to 'true', nothing to do.
[5/8]: activating sidgen task
[6/8]: restarting Directory Server to take MS PAC and LDAP plugins changes into account
[7/8]: adding fallback group
[8/8]: adding SIDs to existing users and groups
This step may take considerable amount of time, please wait..
Done.
Configuring client side components
This program will set up IPA client.
Version 4.9.11
Using existing certificate '/etc/ipa/ca.crt'.
Client hostname: ipa.home.lab
Realm: HOME.LAB
DNS Domain: home.lab
IPA Server: ipa.home.lab
BaseDN: dc=home,dc=lab
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Adding SSH public key from /etc/openssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/openssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/openssh/ssh_host_dsa_key.pub
Adding SSH public key from /etc/openssh/ssh_host_rsa_key.pub
Configured passwd in /etc/nsswitch.conf
Configured group in /etc/nsswitch.conf
Configured netgroup in /etc/nsswitch.conf
Configured automount in /etc/nsswitch.conf
Configured services in /etc/nsswitch.conf
Configured sudoers in /etc/nsswitch.conf
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/openssh/ssh_config
Configured /etc/openssh/sshd_config
Configuring home.lab as NIS domain.
Client configuration complete.
Could not remove /tmp/.private/root/tmpeg64ffqa.ipabkp
The ipa-client-install command was successful
Invalid IP address fe80::5054:ff:feb7:a4fb for ipa.home.lab.: cannot use link-local IP address fe80::5054:ff:feb7:a4fb
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
2. You can now obtain a kerberos ticket using the command: 'kinit admin'
This ticket will allow you to use the IPA tools (e.g., ipa user-add)
and the web user interface.
Be sure to back up the CA certificates stored in /root/cacert.p12
These files are required to create replicas. The password for these
files is the Directory Manager password
The ipa-server-install command was successful
Когда дайдёт до The ipa-server-install command was successful можно провести проверку:
# kinit admin
Password for [email protected]:
# klist
Ticket cache: KEYRING:persistent:0:0
Default principal: [email protected]
Valid starting Expires Service principal
16.12.2023 11:54:08 17.12.2023 11:50:46 krbtgt/[email protected]
Статус всех подсистем FreeIPA:
[root@ipa ~]# ipactl status
Directory Service: RUNNING
krb5kdc Service: RUNNING
kadmin Service: RUNNING
named Service: RUNNING
httpd Service: RUNNING
ipa-custodia Service: RUNNING
pki-tomcatd Service: RUNNING
ipa-otpd Service: RUNNING
ipa-dnskeysyncd Service: RUNNING
ipa: INFO: The ipactl command was successful
[root@ipa ~]#
Как видим билет Kerberos получили, все сервисы запущены.
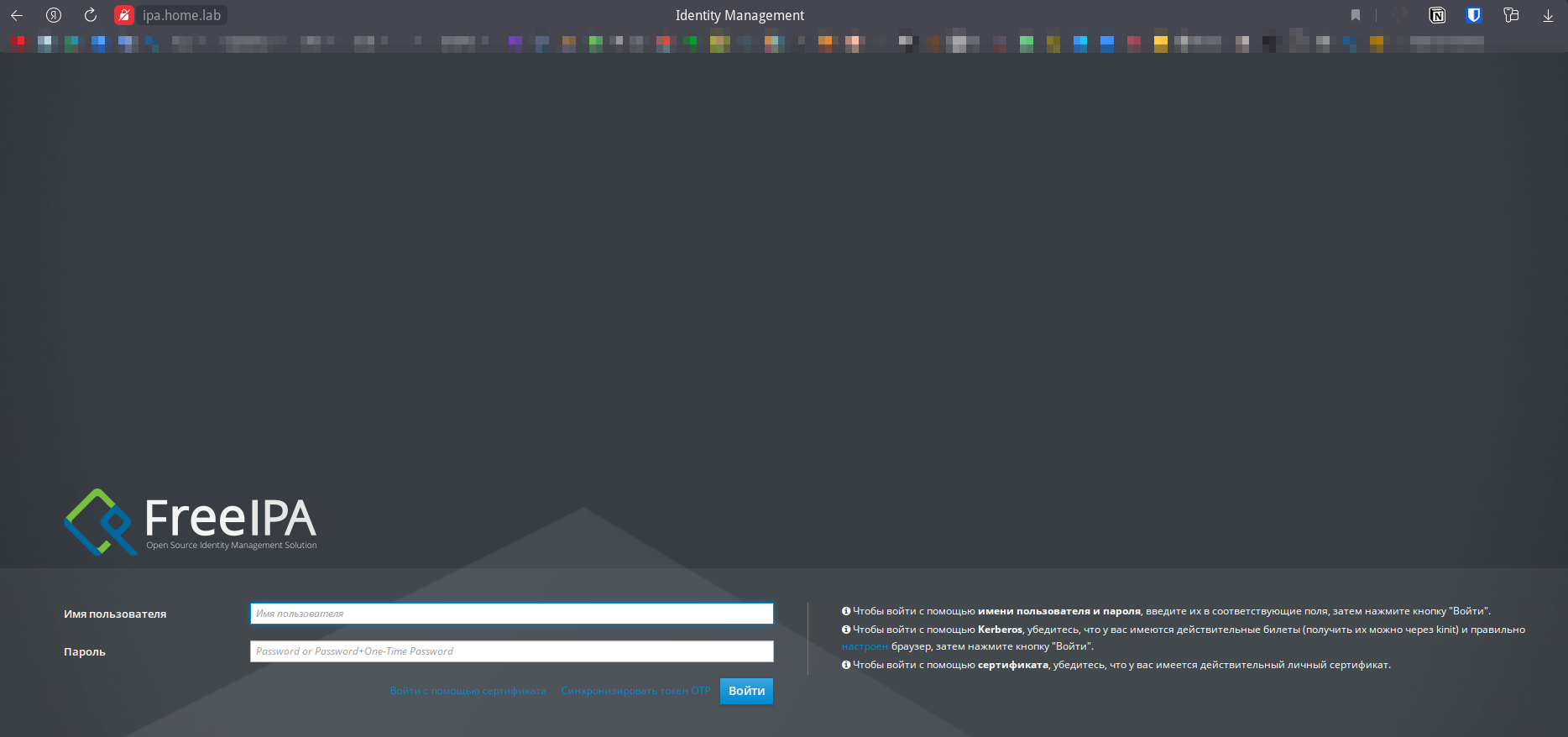
Попробуем подключиться к веб интерфейсу администрирования https://ipa.home.lab/ логин admin и пароль который мы ранее задали в параметре IPA admin password.
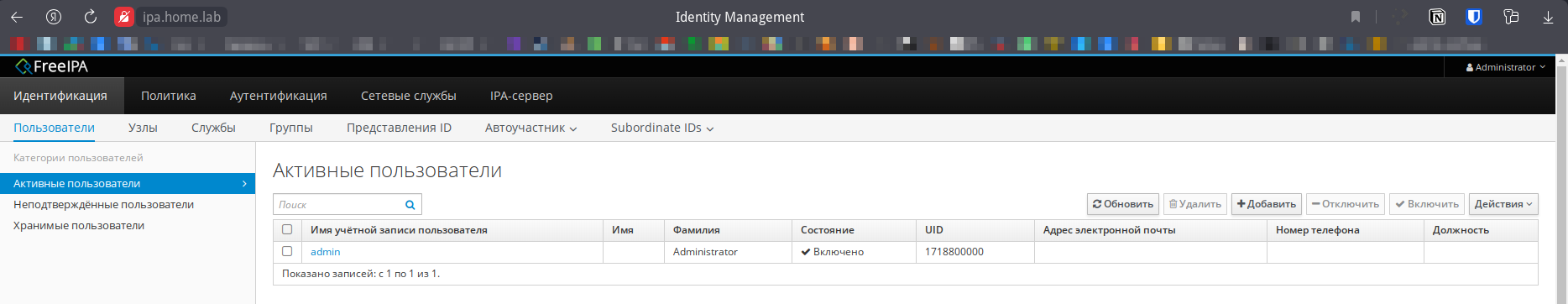
После авторизации мы должны увидеть нашего пока единственного пользователя:
Настройка клиента¶
Также как и на сервере зададим хостнейм и для клиента:
Устанавливаем пакет для клиента FreeIPA:
Подключаем нашего клиента к FreeIPA:
# ipa-client-install --mkhomedir --domain home.lab --realm HOME.LAB --enable-dns-updates
This program will set up IPA client.
Version 4.9.11
Discovery was successful!
Do you want to configure CHRONY with NTP server or pool address? [no]:
Client hostname: client1.home.lab
Realm: HOME.LAB
DNS Domain: home.lab
IPA Server: ipa.home.lab
BaseDN: dc=home,dc=lab
Continue to configure the system with these values? [no]: yes
Attempting to sync time with CHRONY
It may take a few seconds
Time successfully synchronized with IPA server
User authorized to enroll computers: admin
Password for [email protected]:
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=HOME.LAB
Issuer: CN=Certificate Authority,O=HOME.LAB
Valid From: 2023-12-16 08:40:31
Valid Until: 2043-12-16 08:40:31
Enrolled in IPA realm HOME.LAB
Created /etc/ipa/default.conf
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Hostname (client1.home.lab) does not have A/AAAA record.
Adding SSH public key from /etc/openssh/ssh_host_rsa_key.pub
Adding SSH public key from /etc/openssh/ssh_host_dsa_key.pub
Adding SSH public key from /etc/openssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/openssh/ssh_host_ed25519_key.pub
Configured passwd in /etc/nsswitch.conf
Configured group in /etc/nsswitch.conf
Configured netgroup in /etc/nsswitch.conf
Configured automount in /etc/nsswitch.conf
Configured services in /etc/nsswitch.conf
Configured sudoers in /etc/nsswitch.conf
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/openssh/ssh_config
Configured /etc/openssh/sshd_config
Configuring home.lab as NIS domain.
Configured /etc/krb5.conf for IPA realm HOME.LAB
Client configuration complete.
The ipa-client-install command was successful
Проверяем работу, для этого пробуем подключиться через ssh под доменным пользователем admin:
$ ssh [email protected]
[email protected]'s password:
$ whoami
admin
$ id
uid=1718800000(admin) gid=1718800000(admins) группы=1718800000(admins)
$ klist
Ticket cache: KEYRING:persistent:1718800000:krb_ccache_DFbjV96
Default principal: [email protected]
Valid starting Expires Service principal
16.12.2023 15:36:41 17.12.2023 14:59:01 krbtgt/[email protected]
Настройка XRDP через SSSD¶
В ALT LINUX 10.2 изменил конфиг /etc/pam.d/common-login и добавил параметры с pam_sss.so в итоге он выглядит так:
#%PAM-1.0
auth required pam_sss.so forward_pass
auth substack system-auth
auth substack system-policy
auth required pam_nologin.so
account required pam_sss.so
account substack system-auth
account substack system-policy
account required pam_nologin.so
password required pam_sss.so
password include system-auth
password include system-policy
session required pam_sss.so
session substack system-auth
session required pam_loginuid.so
-session optional pam_systemd.so
session substack system-policy
При подключении через RDP столкнулся с ошибкой, где аутентификация через sssd проходит:
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: pam_sss(xrdp-sesman:auth): authentication success; logname= uid=0 euid=0 tty=xrdp-sesman ruser= rhost= user=daffin
а логин в систему нет:
дек 17 13:09:47 srv-job.home.lab xrdp[6866]: [INFO ] login failed for user daffin
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: [INFO ] Socket 12: AF_INET connection received from 127.0.0.1 port 36088
дек 17 13:09:47 srv-job.home.lab xrdp[6866]: [INFO ] xrdp_wm_log_msg: sesman connect ok
дек 17 13:09:47 srv-job.home.lab xrdp[6866]: [INFO ] sesman connect ok
дек 17 13:09:47 srv-job.home.lab xrdp[6866]: [INFO ] sending login info to session manager. Please wait...
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: pam_sss(xrdp-sesman:auth): authentication success; logname= uid=0 euid=0 tty=xrdp-sesman ruser= rhost= user=daffin
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: pam_sss(xrdp-sesman:auth): authentication success; logname= uid=0 euid=0 tty=xrdp-sesman ruser= rhost= user=daffin
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: [INFO ] login denied for user daffin
дек 17 13:09:47 srv-job.home.lab xrdp[6866]: [INFO ] xrdp_wm_log_msg: login failed for user daffin
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: [ERROR] sesman_data_in: scp_process_msg failed
дек 17 13:09:47 srv-job.home.lab xrdp[6866]: [INFO ] login failed for user daffin
дек 17 13:09:47 srv-job.home.lab xrdp-sesman[6859]: [ERROR] sesman_main_loop: trans_check_wait_objs failed, removing trans
дек 17 13:09:49 srv-job.home.lab xrdp[6866]: [ERROR] xrdp_iso_send: trans_write_copy_s failed
дек 17 13:09:49 srv-job.home.lab xrdp[6866]: [ERROR] Sending [ITU T.125] DisconnectProviderUltimatum failed
Не стал углубляться в подробности, по какой причине XRDP не видит группу tsusers, хотя она есть:
$ id daffin
uid=1718800003(daffin) gid=1718800010(share) группы=1718800010(share),1718800011(tsusers),1718800006(users),1718800007(sudo),1718800004(samba),1718800008(wheel)
Просто в файле /etc/xrdp/sesman.ini закомментировал строки:
и перезапустил сервис:Также из нюансов для Альта заметил, что не работает выполнение sudo и su, хотя в том же дебиане всё работает. Выполнил следующие команды:
Настройка Synology¶
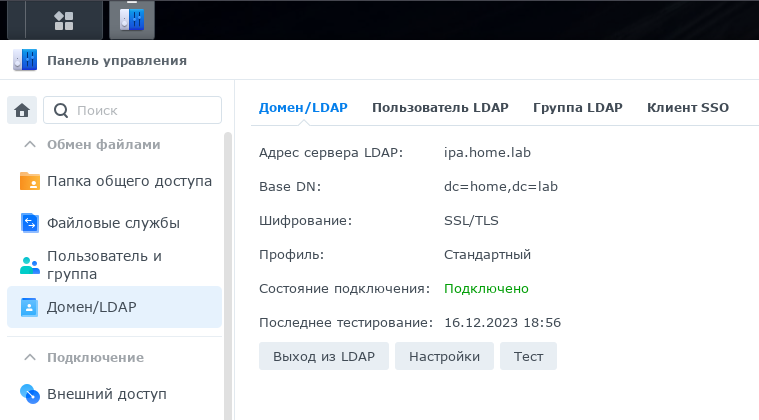
Тут всё довольно таки просто. На стороне https://ipa.home.lab/ создал пользователя synology. Далее переходим в раздел Панель управления -> Домен/LDAP и указываем данные, к сожалению, не сделал скрин, а выходить из настроенного LDAP не хочется, единственный момент в поле Bind DN указывал:
uid=synology,cn=users,cn=compat,dc=home,dc=lab
По итогу должно выглядеть примерно так:
Полезные команды¶
-
Поменять дефолтный шел
-
SSSD имеет кэш, который он использует для хранения данных о пользователях, группах и других объектах. Кэш используется для повышения производительности за счет сокращения количества обращений SSSD к поставщику удостоверений. Чтобы очистить SSSD-кэш, вы можете использовать команду sss_cache. Например: